Visualized Censorship in China
A picture is worth a thousand words. The origin of this popular phrase may in fact be the Chinese proverb 一畫勝千言. So what would be a better way to communicate our analysis of the current online censorship in China than just that, in pictures? The wonderful online tool Wordle helped us do just that. If you click on any of the images you will see a larger version.
Websites blocked in China
First out is a visualization of major websites blocked in China. This was made using this list and by using the popularity of the website to give it more or less weight.

Searches blocked in China
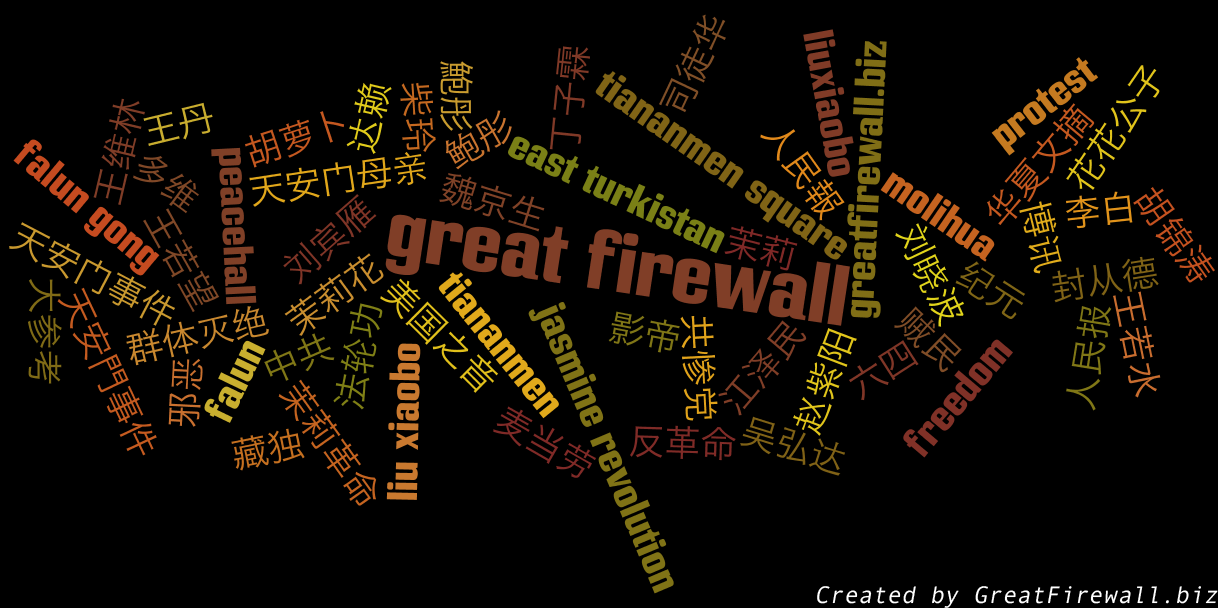
Next up is a visualization of blocked searches. These are words and phrases deemed sensitive, meaning that if you search for any of them in Google while in China your connection will be reset and you'll only see a blank page. If you think the list is incomplete, please help us by adding a new search for testing.
All together
Our final visualization is a combination of major websites as well as searches blocked in China. If you have any ideas for other types of visualizations please feel free to comment.

