GreatFire June: Bloomberg Blocked As Well As Hundreds Of Additional Keywords On Weibo
The big question for people following online censorship in China is a simple: is censorship increasing or decreasing in China? Many cite the growth of microblogs such as Sina Weibo, as well as the total number of Internet users in China, and argue that while censorship is pervasive, overall, things are opening up. However, two developments during the month of June suggest otherwise. The first was that Bloomberg was blocked, the first time in years that a major, English-language news website was blocked. The second was that out of the 15,000+ keywords on Sina Weibo, Google and Wikipedia that we are monitoring, an additional 231 were blocked while only 24 were unblocked. It would seem that the grip on censorship is tightening.
In a curious incident, Henan News published a story mentioning the Great Firewall by name both in Chinese and English. The story was quickly deleted, but thanks to Google Cache you can still view it here.
Bloomberg Blocked - More To Come?
 http://www.bloomberg.com was blocked on June 29. As a major, English-language news website, this means that Bloomberg has been singled out by the Chinese authorities. This followed a lengthy report by Bloomberg on the family wealth of Xi Jinping, the man presumed to replace Hu Jintao as Chairman of the Communist Party later this year. The obvious reason for blocking Bloomberg would be to prevent Chinese netizens from reading the story in the first place. This is not all that effective however, since blocking it only brought more attention to the story, and much of the content of the story could soon be found on other foreign media websites which themselves were not blocked. The authorities could have blocked access to the story without blocking Bloomberg altogether, as they did with a story in The Economist about the Bloomberg story on Xi Jinping. Another interpretation is that the authorities wanted to send a warning to foreign journalists in China: don't go too far, or we'll block you altogether, because bloomberg China http://www.bloomberg.cn/ which is a technical site and contains no reports of Xi Jingping is blocked even though it acquired an ICP license from Chinese authority , That would also be supported by the expulsion of a foreign journalist in May, the first such action since 1998. We could likely write a separate post on how foreign news organizations agree to self-censor their content in exchange for market access in China but for the purposes of this story we will assume that the authorities block the content that they want to block.
http://www.bloomberg.com was blocked on June 29. As a major, English-language news website, this means that Bloomberg has been singled out by the Chinese authorities. This followed a lengthy report by Bloomberg on the family wealth of Xi Jinping, the man presumed to replace Hu Jintao as Chairman of the Communist Party later this year. The obvious reason for blocking Bloomberg would be to prevent Chinese netizens from reading the story in the first place. This is not all that effective however, since blocking it only brought more attention to the story, and much of the content of the story could soon be found on other foreign media websites which themselves were not blocked. The authorities could have blocked access to the story without blocking Bloomberg altogether, as they did with a story in The Economist about the Bloomberg story on Xi Jinping. Another interpretation is that the authorities wanted to send a warning to foreign journalists in China: don't go too far, or we'll block you altogether, because bloomberg China http://www.bloomberg.cn/ which is a technical site and contains no reports of Xi Jingping is blocked even though it acquired an ICP license from Chinese authority , That would also be supported by the expulsion of a foreign journalist in May, the first such action since 1998. We could likely write a separate post on how foreign news organizations agree to self-censor their content in exchange for market access in China but for the purposes of this story we will assume that the authorities block the content that they want to block.
At almost the same time, the New York Times launched a Chinese edition of it's website, which has so far not been blocked. The fact that most other Chinese versions of foreign media websites are blocked suggest that this is just a question of time. Also, as we reported on July 3, the Weibo accounts of the New York Times were quickly closed on both Sina and Tencent.
Here's an overview of major news websites and which ones are currently blocked. We'll follow their progress with great interest.
| English Website | Chinese Website | Comments |
|---|---|---|
| http://www.bbc.co.uk | http://www.bbc.co.uk/zhongwen | |
| http://www.bloomberg.com | - | |
| - | http://www.boxun.com | |
| http://chinadigitaltimes.net | http://chinadigitaltimes.net/chinese | |
| http://www.cnn.com | - | |
| http://www.economist.com | - | |
| http://www.ft.com | http://www.ftchinese.com | Individual articles on the Chinese edition such as this one are blocked. |
| http://www.guardian.co.uk | - | |
| http://www.huffingtonpost.com | - | |
| http://www.nytimes.com | http://cn.nytimes.com | Launched in June, 2012. Will it be blocked? |
| http://www.scmp.com | - | |
| http://www.voanews.com | http://www.voachinese.com | |
| http://wsj.com | http://cn.wsj.com |
Google (Quietly) Continues To Bring Transparency To Censorship
 As we reported last month, Google launched a new feature which notifies users trying to search for certain keywords that would otherwise be blocked by the Great Firewall. The new function was quickly disabled by the Chinese authorities by blocking access to the javascript file in which it was defined. Since then, Google has cleverly responded by embedding all the required code and data of what's blocked in the html file. This makes it difficult for the Great Firewall to disable this transparency function without blocking Google altogether. So far, they've done nothing and as this is written the feature is working in China.
As we reported last month, Google launched a new feature which notifies users trying to search for certain keywords that would otherwise be blocked by the Great Firewall. The new function was quickly disabled by the Chinese authorities by blocking access to the javascript file in which it was defined. Since then, Google has cleverly responded by embedding all the required code and data of what's blocked in the html file. This makes it difficult for the Great Firewall to disable this transparency function without blocking Google altogether. So far, they've done nothing and as this is written the feature is working in China.
If Google wants to, they could take this much further. If a user clicks on a URL known to be blocked, for example, they could inform the user and even offer suggestions of ways around the censorship. We'll keep following the Google vs Great Firewall battle closely.
Unblocked Foreign Websites Keep Getting Faster
As can be seen in the chart below, foreign websites that are not blocked continue the trend of getting faster in China. The data is based on average download speed of Alexa Top 500 websites not hosted in China, per month.
Keywords Blocked And Unblocked
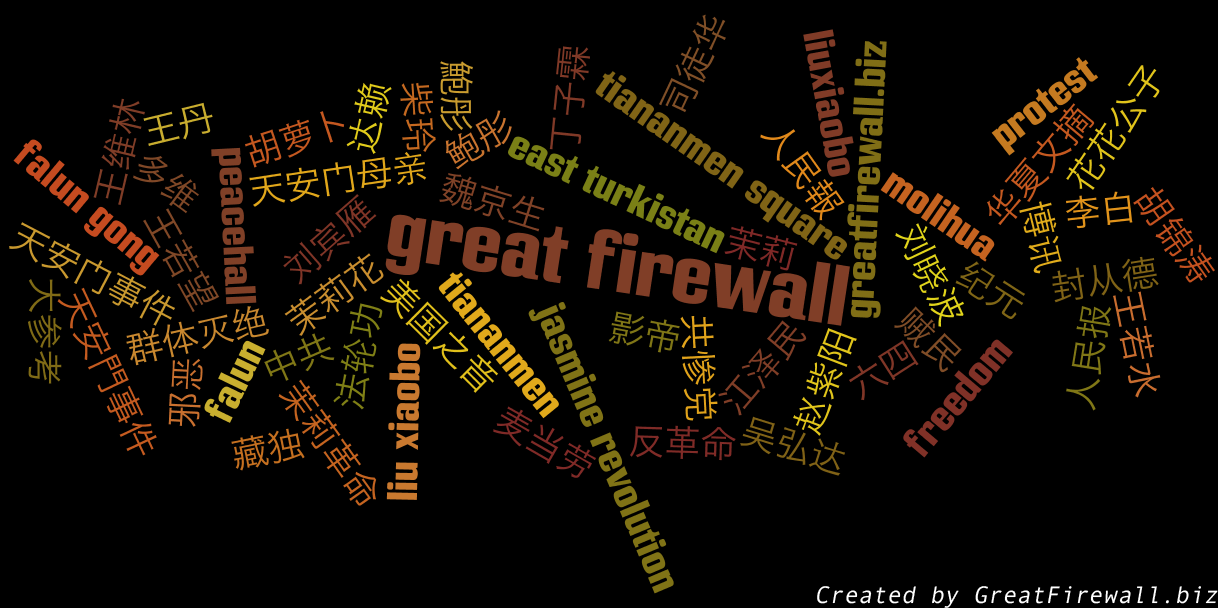 Below is a list of 231 unique keywords that were blocked in June. Only keywords that we know were not blocked before June are included. Also, there's a list of 24 keywords that were previously blocked, and were unblocked during June. As always, if you think anything is missing, please add it to our database for testing using the search bar on the top of this page. All URLs and keywords in our database are continously tested so that we can detect changes.
Below is a list of 231 unique keywords that were blocked in June. Only keywords that we know were not blocked before June are included. Also, there's a list of 24 keywords that were previously blocked, and were unblocked during June. As always, if you think anything is missing, please add it to our database for testing using the search bar on the top of this page. All URLs and keywords in our database are continously tested so that we can detect changes.
- Blocked
- {{google:法拉利车祸}}
- {{weibo:21世纪中国基金会}}
- {{weibo:4 june}}
- {{weibo:512228}}
- {{weibo:FreeTibet}}
- {{weibo:Ninecommentaries}}
- {{weibo:UltraSurf}}
- {{weibo:bignews}}
- {{weibo:bo xilai}}
- {{weibo:boxun}}
- {{weibo:creaders}}
- {{weibo:dajiyuan.com}}
- {{weibo:demolish}}
- {{weibo:epochtimes}}
- {{weibo:freedom}}
- {{weibo:freenet}}
- {{weibo:hrichina}}
- {{weibo:minghui}}
- {{weibo:peacehall}}
- {{weibo:q=cache}}
- {{weibo:q=天灭}}
- {{weibo:renminbao}}
- {{weibo:safeweb}}
- {{weibo:tankman}}
- {{weibo:tiananmen}}
- {{weibo:tianwang}}
- {{weibo:without forced demolitions there can be no new china}}
- {{weibo:xinsheng}}
- {{weibo:zhengjian}}
- {{weibo:丁子霖}}
- {{weibo:丁子霖}}
- {{weibo:不明真相的群众}}
- {{weibo:世维会}}
- {{weibo:东南西北论谈}}
- {{weibo:东土耳其斯坦}}
- {{weibo:东西南北论坛}}
- {{weibo:两岸三地论坛}}
- {{weibo:中共}}
- {{weibo:中功}}
- {{weibo:中南海}}
- {{weibo:中国论坛}}
- {{weibo:中央警卫团}}
- {{weibo:亡党}}
- {{weibo:人民之声论坛}}
- {{weibo:人民内情真相}}
- {{weibo:代开发票}}
- {{weibo:代理}}
- {{weibo:伍凡}}
- {{weibo:你说我说论坛}}
- {{weibo:倒台}}
- {{weibo:先皇}}
- {{weibo:党国}}
- {{weibo:党委书记}}
- {{weibo:党棍}}
- {{weibo:公开信}}
- {{weibo:公惨档}}
- {{weibo:共产}}
- {{weibo:共铲}}
- {{weibo:关键时刻}}
- {{weibo:冤民大同盟}}
- {{weibo:刘延东}}
- {{weibo:动态网}}
- {{weibo:北京之春}}
- {{weibo:北国之春}}
- {{weibo:华夏文摘}}
- {{weibo:华岳时事论坛}}
- {{weibo:华语世界论坛}}
- {{weibo:华通时事论坛}}
- {{weibo:南大自由论坛}}
- {{weibo:历史的伤口}}
- {{weibo:反社会}}
- {{weibo:反腐败论坛}}
- {{weibo:发票代开}}
- {{weibo:台湾政论区}}
- {{weibo:台湾自由联盟}}
- {{weibo:台湾青年 独立联盟}}
- {{weibo:台湾青年独立联盟}}
- {{weibo:司徒华}}
- {{weibo:善恶有报}}
- {{weibo:因言获罪}}
- {{weibo:国家防火墙}}
- {{weibo:国新办}}
- {{weibo:国母}}
- {{weibo:地下刊物}}
- {{weibo:地下教会}}
- {{weibo:大中华论坛}}
- {{weibo:大参考}}
- {{weibo:大家论坛}}
- {{weibo:天安門}}
- {{weibo:天安门之魂}}
- {{weibo:天安门事变}}
- {{weibo:天安门城楼罚站}}
- {{weibo:天安门录影带}}
- {{weibo:天安门清场}}
- {{weibo:天安门被清场}}
- {{weibo:天怒}}
- {{weibo:太子}}
- {{weibo:夺权}}
- {{weibo:学联}}
- {{weibo:学自联}}
- {{weibo:学运}}
- {{weibo:宪章}}
- {{weibo:工自联}}
- {{weibo:广场上的热血}}
- {{weibo:庆红}}
- {{weibo:开枪}}
- {{weibo:异见人士}}
- {{weibo:异议人士}}
- {{weibo:张宏堡}}
- {{weibo:张斌}}
- {{weibo:张高丽}}
- {{weibo:影帝}}
- {{weibo:徐才厚}}
- {{weibo:总书记}}
- {{weibo:总理的意思是5月份开始下跌}}
- {{weibo:我没有敌人}}
- {{weibo:戒严}}
- {{weibo:打砸烧事件}}
- {{weibo:抗议}}
- {{weibo:改革历程}}
- {{weibo:政治体制改革}}
- {{weibo:文字狱}}
- {{weibo:新华通论坛}}
- {{weibo:新右派}}
- {{weibo:新生网}}
- {{weibo:新疆独立}}
- {{weibo:新观察论坛}}
- {{weibo:方滨兴}}
- {{weibo:无界}}
- {{weibo:暴乱}}
- {{weibo:暴力拆迁}}
- {{weibo:暴动}}
- {{weibo:暴徒}}
- {{weibo:暴政}}
- {{weibo:曹长青}}
- {{weibo:木子论坛}}
- {{weibo:木犀地}}
- {{weibo:朱镕基}}
- {{weibo:梦萦未名湖}}
- {{weibo:正义党论坛}}
- {{weibo:正念}}
- {{weibo:正见网}}
- {{weibo:民主墙}}
- {{weibo:民主女神}}
- {{weibo:民联}}
- {{weibo:民运}}
- {{weibo:民进党}}
- {{weibo:民阵}}
- {{weibo:河殇}}
- {{weibo:法拉利车祸}}
- {{weibo:泽民}}
- {{weibo:洗脑}}
- {{weibo:洪吟}}
- {{weibo:洪哲胜}}
- {{weibo:活摘器官}}
- {{weibo:淋巴县长}}
- {{weibo:温总}}
- {{weibo:温爷爷}}
- {{weibo:游行}}
- {{weibo:热站政论网}}
- {{weibo:煽动不明真相的月亮}}
- {{weibo:独立台湾}}
- {{weibo:王炳章}}
- {{weibo:盛雪}}
- {{weibo:红色恐怖}}
- {{weibo:纪元}}
- {{weibo:纳米比亚}}
- {{weibo:经文}}
- {{weibo:网特}}
- {{weibo:网管办}}
- {{weibo:罗干}}
- {{weibo:罢课}}
- {{weibo:罢餐}}
- {{weibo:群体灭绝}}
- {{weibo:老人政治}}
- {{weibo:老江}}
- {{weibo:老胡}}
- {{weibo:自焚}}
- {{weibo:良心犯}}
- {{weibo:艾末末}}
- {{weibo:艾神}}
- {{weibo:花园网}}
- {{weibo:花花公子}}
- {{weibo:苏家屯}}
- {{weibo:苏绍智}}
- {{weibo:茅于轼}}
- {{weibo:茉莉}}
- {{weibo:蔡名照}}
- {{weibo:薛飞}}
- {{weibo:蛤蟆}}
- {{weibo:蟹农场}}
- {{weibo:西藏流亡政府}}
- {{weibo:记者无疆界}}
- {{weibo:诺贝尔和平奖}}
- {{weibo:贼民}}
- {{weibo:超越红墙}}
- {{weibo:路青}}
- {{weibo:辛子陵}}
- {{weibo:辛灏年}}
- {{weibo:迪里夏提}}
- {{weibo:迫害}}
- {{weibo:追查国际}}
- {{weibo:邓小平}}
- {{weibo:邪恶}}
- {{weibo:酷刑}}
- {{weibo:阅后即焚}}
- {{weibo:防火长城}}
- {{weibo:阿波罗新闻网}}
- {{weibo:阿波罗网}}
- {{weibo:陈一谘}}
- {{weibo:陈破空}}
- {{weibo:陈西}}
- {{weibo:集会}}
- {{weibo:雪山狮子}}
- {{weibo:零八纲领}}
- {{weibo:青天白日旗}}
- {{weibo:静坐}}
- {{weibo:非正常死亡}}
- {{weibo:非法献花,非法吃喝,非法默哀,非法xx}}
- {{weibo:革命}}
- {{weibo:韩东方}}
- {{weibo:马三家}}
- {{weibo:马凯}}
- {{weibo:驾崩}}
- {{weibo:高智晟}}
- {{weibo:高瞻}}
- {{weibo:高自联}}
- {{weibo:鮑彤}}
- {{weibo:鲁昕}}
- {{weibo:黄祸}}
- {{weibo:黎安友}}
- Unblocked
- {{google:64之后}}
- {{google:轮奸}}
- {{google:百家争鸣}}
- {{google:宪法35条}}
- {{google:占领北京}}
- {{google:伊斯兰教}}
- {{google:牧函}}
- {{google:GCD}}
- http://en.wikipedia:Boxer_Rebellion
- {{weibo:426社论}}
- {{weibo:64}}
- {{weibo:gongchan当}}
- {{weibo:gongchan挡}}
- {{weibo:gongchan裆}}
- {{weibo:li changchun}}
- {{weibo:wangce}}
- {{weibo:wangce}}
- {{weibo:人权不能完全保障}}
- {{weibo:八八}}
- {{weibo:坦克}}
- {{weibo:猥亵}}
- {{weibo:盲人}}
- {{weibo:长安街}}
- {{weibo:黑瞎子岛}}
Other Notable Changes
Do you remember http://myspace.com? At least the people in charge of the Great Firewall seem to - they blocked it last month. On the other hand, http://www.rapidshare.com was unblocked at least as of June 1. http://www.bitly.com was blocked at least as of June 24 but the shorter domain http://bit.ly which is used for short links is still not blocked.
