Eight Questions For GlobalWebIndex
GlobalWebIndex published a new report on Internet usage around the world this week, and it contained some great news for China. Twitter, Facebook and Google+ have increased their user numbers dramatically in China, as seen below. There's just one problem. They are all blocked in China, and we believe that GlobalWebIndex has got its data wrong (as do TheNextWeb):
This development is what we hope happens in China's future and it's what we are fighting for but it certainly is not the reality now. The last thing we want to see is people saying that Chinese netizens have free and open access to social media around the world. They don't! They are prevented from looking at many foreign web sites and they are also prevented from accessing information on Chinese web sites. The Great Firewall is not some myth, it's a sad reality. Chinese censorship authorities will be delighted to see this news as it makes the rest of the world believe that censorship is not happening here.
Because of this, we want to ask GlobalWebIndex the following 8 questions:
- How many registered users are there from China for Twitter, Facebook and Google+? Your own data and tweets suggest 70 million for Twitter (via your tweet), 125 million for Facebook (also via your tweet although slide 17 of your report suggests 450 million) and 150 million for Google + (via the same report).
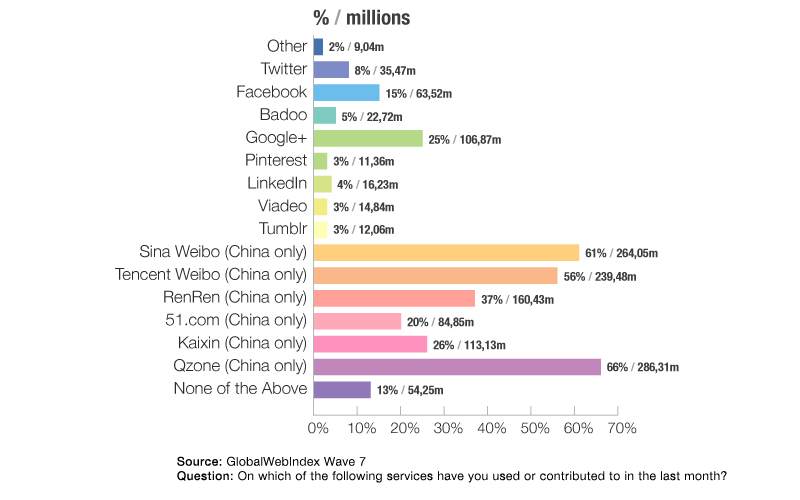
- How many of those users are active? Your data again suggests 35.4 million Twitter users (via your blog post) but eMarketer suggests 35.5 million (via their infographic). Facebook at 63 million and Google + at 106 million (both via your infographic). How do the active user percentages for Twitter (47%), Facebook (50%) and Google + (71%) compare to other markets?
- Does China include Hong Kong, Macau and/or Taiwan in your reports?
- If Twitter has more active users in China than in the US, how come the most popular account based in China has only 562,250 followers (and is run by a foreigner)? This compares to the most followed US-based Twitter account (@ladygaga: 29m followers) as well as the most followed Sina Weibo account (姚晨: 24m followers), both more than 100 times more popular.
- If Facebook has tens of millions of users in China, why do they themselves only claim to have 600k?
- If LinkedIn.com has 16m users in China and Facebook has four times as many, why does Alexa rank LinkedIn as #267 and Facebook only as #482?
- What is a “Virtual Cloud Network” and how do you use it to circumvent censorship? Did you ask users how they get around the Great Firewall? In our experience, free circumvention tools such as Ultrasurf and Freegate are more widespread than commercial VPNs but we lack data and it would be very interesting to know more.
- How did you/Lightspeed find users to reply to your surveys in China? Was the survey in Chinese? If so, how were the names of Facebook, Twitter, Google+ and LinkedIn translated? On what websites was it advertised? Was the survey website itself blocked or throttled in China?